Clickatell Blog
Conversational Marketing
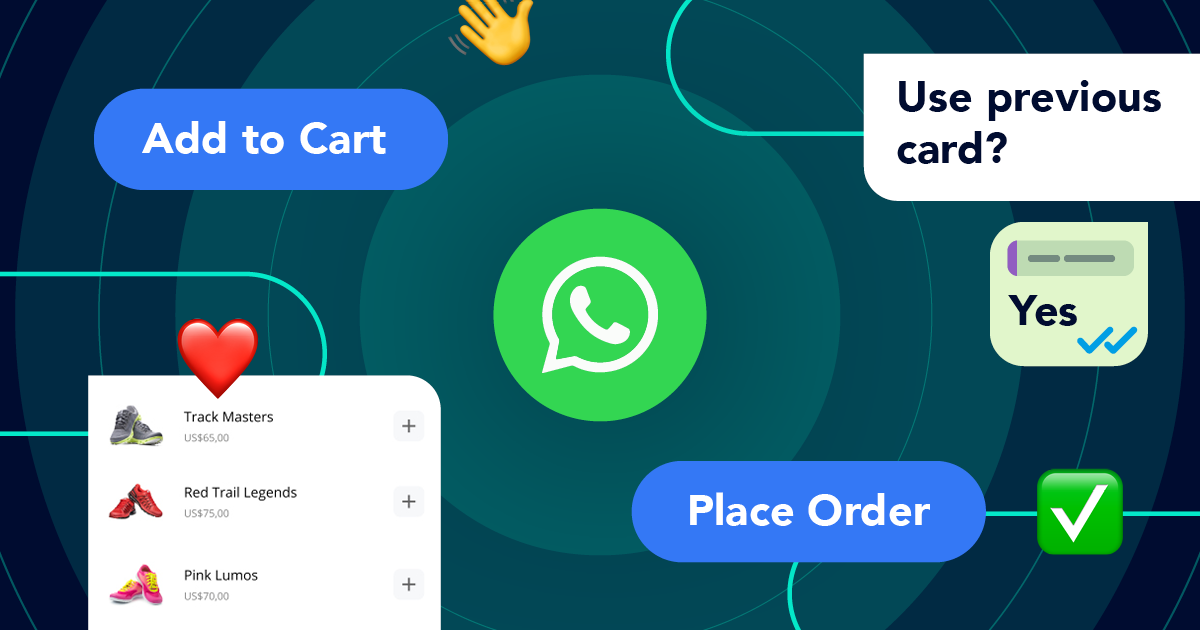
Put your best foot forward with conversational marketing on WhatsAppLearn how to build WhatsApp user journeys for better engagement and convenient end-to-end digital commerce experiences.Read MoreMost Recent
Step into the future of business messaging.
SMS and two-way channels, automation, call center integration, payments - do it all with Clickatell's Chat Commerce platform.
New